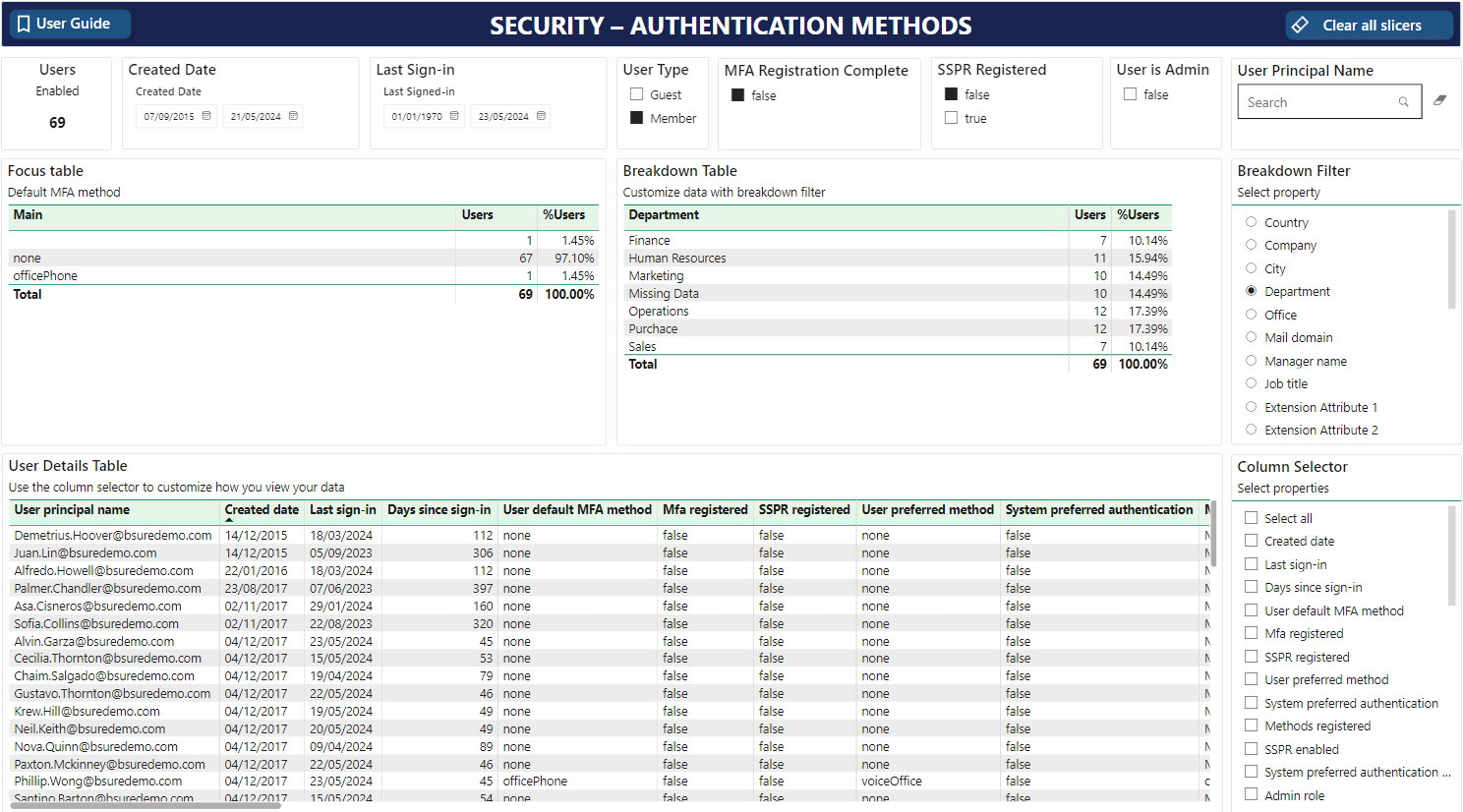
It is common to find many accounts with this status. These users are normally accounts that hasn't been used in many years, and service accounts etc.
It is common to find many accounts with this status. These users are normally accounts that hasn't been used in many years, and service accounts etc.